Getty Images
On March 1, Russian forces invading Ukraine took out a TV tower in Kyiv after the Kremlin declared its intention to destroy “disinformation” in the neighboring country. That public act of kinetic destruction accompanied a much more hidden but no less damaging action: targeting a prominent Ukrainian broadcaster with malware to render its computers inoperable.
The dual action is one of many examples of the “hybrid war” Russia has waged against Ukraine since before the invasion began, according to a report published Wednesday by Microsoft. Shortly before the invasion, the company said, hackers in six groups aligned with the Kremlin have launched no fewer than 237 operations in concert with the physical attacks on the battlefield. Almost 40 of them targeting hundreds of systems used wiper malware, which deletes essential files stored on hard drives so the machines can’t boot.
“As today’s report details, Russia’s use of cyberattacks appears to be strongly correlated and sometimes directly timed with its kinetic military operations targeting services and institutions crucial for civilians,” Tom Burt, Microsoft corporate vice president for customer security, wrote. He said the “relentless and destructive Russian cyberattacks” were particularly concerning because many of them targeted critical infrastructure that could have cascading negative effects on the country.
It’s not clear if the Kremlin is coordinating cyber operations with kinetic attacks or if they’re the result of independent bodies pursuing a common goal of disrupting or degrading Ukraine’s military and government while undermining citizens’ trust in those institutions. What’s undeniable is that the two components in this hybrid war have complemented each other.
Examples of Russian cyber actions correlating to political or diplomatic development taken against Ukraine before the invasion began include:
- The deployment of wiper malware dubbed WhisperGate on a “limited number” of Ukrainian government and IT sector networks on January 3 and the defacement and DDoSing of Ukrainian websites a day later. Those actions came as diplomatic talks between Russia and Ukrainian allies broke down.
- DDoS attacks waged on Ukrainian financial institutions on February 15 and February 16. On February 17, the Kremlin said it would be “forced to respond” with military-technical measures if the US didn’t capitulate to Kremlin demands.
- The deployment on February 23 of wiper malware by another Russian state group on hundreds of Ukrainian systems in the government, IT, energy, and financial sectors. Two days earlier, Putin recognized the independence of Ukrainian separatists aligned with Russia.
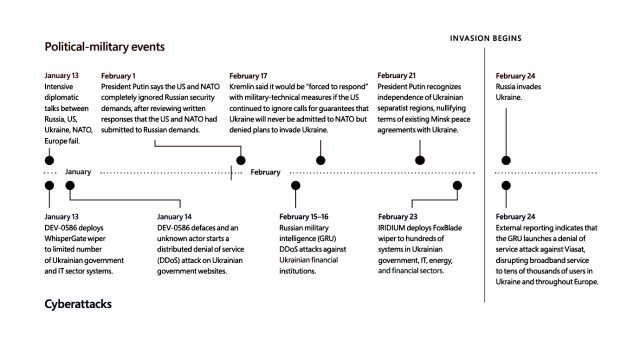
Microsoft
Russia stepped up its cyber offensive once the investigation began. Highlights include:
-
- The February 14 and February 17 compromises of critical infrastructure in the Ukrainian cities of Odesa and Sumy. These actions appeared to have set the stage for February 24, when Russian tanks advanced into Sumy.
- On March 2, Russian hackers burrowed into the network of a Ukrainian nuclear power company. A day later, Russian forces occupied Ukraine’s biggest nuclear power station.
- On March 11, a government agency in Dnipro was targeted with a destructive implant. The same day, Russian forces launched strikes into Dnipro government buildings.
Wednesday’s report said that as early as March 2021, hackers aligned with Russia prepared for conflict with its neighboring country by escalating actions against organizations inside or aligned with Ukraine.
The actions haven’t stopped since. Burt wrote:
When Russian troops first started to move toward the border with Ukraine, we saw efforts to gain initial access to targets that could provide intelligence on Ukraine’s military and foreign partnerships. By mid-2021, Russian actors were targeting supply chain vendors in Ukraine and abroad to secure further access not only to systems in Ukraine but also NATO member states. In early 2022, when diplomatic efforts failed to de-escalate mounting tensions around Russia’s military build-up along Ukraine’s borders, Russian actors launched destructive wiper malware attacks against Ukrainian organizations with increasing intensity. Since the Russian invasion of Ukraine began, Russian cyberattacks have been deployed to support the military’s strategic and tactical objectives. It’s likely the attacks we’ve observed are only a fraction of activity targeting Ukraine.
The report includes a variety of security measures likely targets of Russian cyberattacks can take to protect themselves. One measure includes turning on a feature called controlled folders. The feature, which isn’t enabled by default, is designed to protect data in specific folders from destruction from ransomware, wipers, and other types of destructive malware.